Those of you who manage Exchange Database Availability Groups, particularly in Exchange 2013, will understand the frustration of coming to the office on a Monday morning to find that your Databases have migrated to A. N. Other server because of some scheduled backup or other task which occurred over the weekend.
To solve this problem, we can configure a Scheduled Task to run the RedistributeActiveDatabases.ps1 script, which will balance your databases out based on the Activation Preference set for each server. Before you configure this task, make sure that your Activation Preference settings are applied as per your desired configuration.
For example, say I have a database named MBDB and two servers named Server1 and Server2 (I’m feeling particularly inventive today). To set the Activation Preference for these database copies, I would run the following Powershell command from EMS:
Set-MailboxDatabaseCopy -identity MBDB\Server1' -ActivationPreference 1 Set-MailboxDatabaseCopy -identity MBDB\Server2' -ActivationPreference 2
This configuration will mean that when I run the RedistributeActiveDatabases.ps1 script, the MBDB database will be moved, if required, to Server1, as long as the required Database Mount Dial setting is achieved (the default setting is Best Availability which requires the Copy Queue Length to be no more than 12).
If I wanted to see how my database copies are currently configured, I would run the following Powershell command from EMS:
Get-MailboxDatabase MBDB | fl server, databaseCopies, activationPreference
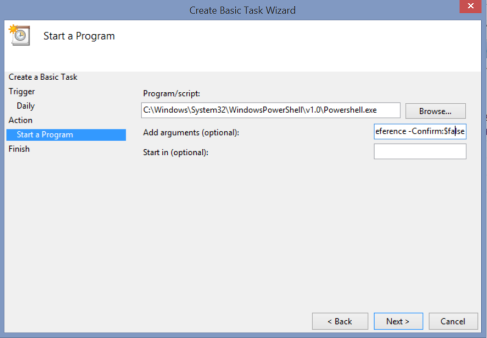
This would show me all the database copies and their Activation Preference. So we now have our settings configured and we want to setup our Scheduled Task. Open your Task Scheduler and create a new Basic Task. Give the task a name and configure your recurrence schedule for the Task. When you get to the Action menu, choose ‘Start a Program’.
Now we need to tell the task to:
1. Launch Powershell
2. Load the Exchange modules and connect to the Exchange server
3. Run the RedistributeActiveDatabases.ps1 script with the correct switches
4. Supress the confirmation dialog which appears when running the script
To do this, we enter the details as follows:
- Program/script:
- C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe
- Add arguments:
- -NonInteractive -WindowStyle Hidden -command “. ‘C:\Program Files\Microsoft\Exchange Server\V15\bin\RemoteExchange.ps1′; Connect-ExchangeServer -auto; .’C:\Program Files\Microsoft\Exchange Server\V15\scripts\RedistributeActiveDatabases.ps1’ -DagName DD-DAG -BalanceDbsByActivationPreference -Confirm:$false”
- Note: Please change the DagName parameter to reference your own DAG!
It looks a little bit like this (OK, it looks just like this):
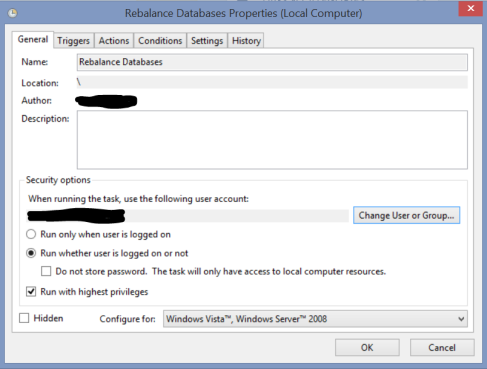
Complete the task creation and then go into the properties of the task. On the General page, configure the task to:
1. Run whether the user is logged on or not
2. Run with highest privileges
3. If need be, change the account running the task to a service account of some kind. That account must be a member of the Organisation Management group
Just like this:
Your Scheduled Task is not configured. You can test it out by manually running it. Hopefully this solves a headache for one or two of you out there!